⚔️ Open-source WAF security testing toolkit — 5,500+ payloads, 25 WAF detections, MCP server for AI workflows
The open-source offensive security toolkit • 5,500+ Payloads • 25 WAF Fingerprints • Zero Dependencies • 61 Tests
Most payload collections are just static text files. Fray is different — it's a structured toolkit that lets you detect, test, and report in seconds:
- 🤖 AI-compatible — structured JSON payloads work well with Claude Code & ChatGPT
- 🔍 Auto-detect which WAF you're facing — 25 vendors fingerprinted instantly
- 📊 One-command reports — professional HTML output with vuln analysis
- 🎯 4,025+ battle-tested payloads — XSS, SQLi, SSRF, SSTI, LLM jailbreaks, and more
- ⚡ Zero config —
pip install frayand you're testing
- Bug bounty hunters — ready-made payloads from real-world disclosures + 120 CVEs
- Red teamers & pentesters — WAF detection → payload selection → report, all in one tool
- Security researchers — structured payloads for bypass research and analysis
- Blue teams — validate your WAF config against 4,000+ real attack patterns
- Students — learn offensive security with guided AI workflows
Fray detects and fingerprints 25 major WAF vendors using header analysis, cookie inspection, response patterns, and error signatures.
| # | WAF Vendor | Detection Method | Key Signatures |
|---|---|---|---|
| 1 | Cloudflare | Headers, Cookies, Error Page | cf-ray, __cfduid, Ray ID pattern |
| 2 | Akamai | Headers, Cookies, Bot Manager | akamai-grn, ak_bmsc, Reference # |
| 3 | AWS WAF | Headers, Cookies, Response Body | x-amzn-waf-action, awsalb, CloudFront |
| 4 | Imperva (Incapsula) | Headers, Cookies, Challenge | x-iinfo, incap_ses, Incident ID |
| 5 | F5 BIG-IP | Headers, Cookies, Error Page | x-wa-info, bigipserver, Support ID |
| 6 | Fastly (Signal Sciences) | Headers, Cookies, Server | x-sigsci-requestid, x-served-by |
| 7 | Microsoft Azure WAF | Headers, Cookies, Front Door | x-azure-fdid, x-azure-ref, arr_affinity |
| 8 | Google Cloud Armor | Headers, Server, reCAPTCHA | x-cloud-trace-context, gfe, Cloud Armor |
| 9 | Barracuda | Headers, Cookies, Server | x-barracuda-url, barra_counter_session |
| 10 | Citrix NetScaler | Headers, Cookies, Server | citrix-transactionid, nsc_, NetScaler |
| 11 | Radware | Headers, Response Text | x-protected-by, AppWall |
| 12 | Palo Alto (Prisma Cloud) | Headers, Response Text | x-pan-, x-prisma |
| 13 | Check Point | Headers, Response Text | x-checkpoint, Check Point |
| 14 | Trustwave (ModSecurity) | Headers, Server, Response | x-mod-security, ModSecurity |
| 15 | Qualys WAF | Headers, Response Text | x-qualys |
| 16 | Penta Security (WAPPLES) | Headers, Cookies | x-wapples, wapples |
| 17 | StackPath | Headers, Server | x-stackpath-shield, StackPath |
| 18 | Sophos | Headers, Response Text | x-sophos, UTM |
| 19 | Scutum | Headers, Response Text | x-scutum |
| 20 | Rohde & Schwarz | Headers, Response Text | x-rs- |
| 21 | Sucuri | Headers, Cookies, Server | x-sucuri-id, sucuri_cloudproxy_uuid |
| 22 | Fortinet FortiWeb | Headers, Cookies, Server | x-fortiweb, fortiwafsid |
| 23 | Wallarm | Headers, Server | x-wallarm-waf-check, nginx-wallarm |
| 24 | Reblaze | Headers, Cookies, Server | x-reblaze-protection, rbzid |
| 25 | Vercel | Headers, Server | x-vercel-id, x-vercel-cache |
# Install from PyPI
pip install fray
# Detect WAF vendor
fray detect https://example.com
# Test with XSS payloads
fray test https://example.com -c xss --max 10
# List all payload categories
fray payloads
# Or clone and use directly
git clone https://github.com/dalisecurity/fray.git
cd fray
python3 waf_tester.py -iPayloadsAllTheThings is a great payload reference. Fray solves a different problem — it's a testing toolkit, not an encyclopedia.
| PayloadsAllTheThings | Fray | |
|---|---|---|
| Format | Markdown docs | Structured JSON (id, description, technique, source) |
| WAF detection | ❌ | ✅ 25-vendor fingerprinting |
| MCP server | ❌ | ✅ 6 tools for AI assistants |
| CLI testing | ❌ Reference only | ✅ fray test <url> -c xss |
| Reports | ❌ | ✅ JSON/HTML with block rate analysis |
| pip install | ❌ | ✅ pip install fray |
| Payload breadth | Deeper | Narrower — value is in tooling |
Real tests that run in CI on every push (Python 3.9–3.13):
| Category | Tests |
|---|---|
| WAF detection logic | 10 (_analyze_signatures with mock data for 4 WAF vendors) |
| MCP server | 13 (tool registration + execution) |
| Payload integrity | 8 (no dupes, no fake data, source provenance) |
| IoT RCE CVEs | 6 (CVE metadata accuracy) |
| CLI commands | 8 |
| Package + loading + reports | 9 |
| Data quality | 2 (no code fragments, no fabricated results) |
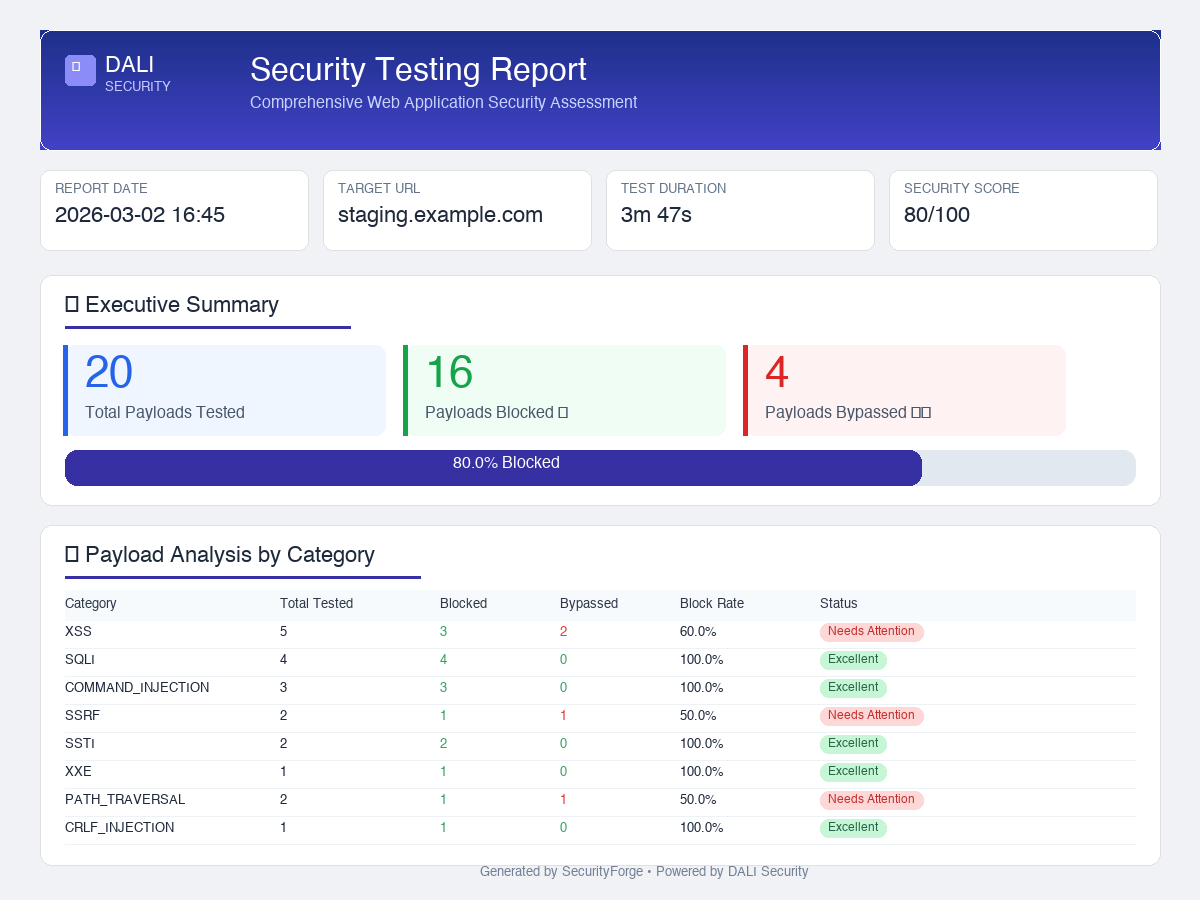
After running a scan, Fray generates a self-contained HTML report you can share with your team or attach to a pentest deliverable.
What's in the report:
- Executive summary — total payloads tested, blocked vs bypassed count, security score
- Block rate progress bar — visual effectiveness metric at a glance
- Category breakdown table — per-category (XSS, SQLi, SSRF, etc.) block rates with status badges
- Vulnerabilities discovered — bypassed payloads grouped by severity (Critical → Low)
- Recommendations — WAF-specific tuning advice and OWASP remediation steps
- Detailed results — full payload-by-payload log with status codes
Export:
fray report --sample # generate a demo report
fray report -i results.json -o report.html # from real scan resultsOutput is a self-contained HTML file — open in any browser or print to PDF.
Fray includes an MCP server that AI assistants can call directly:
pip install fray[mcp]
fray mcp6 MCP tools: list_payload_categories, get_payloads, search_payloads, get_waf_signatures, get_cve_details, suggest_payloads_for_waf
Configure Claude Desktop (~/Library/Application Support/Claude/claude_desktop_config.json):
{
"mcpServers": {
"fray": {
"command": "python",
"args": ["-m", "fray.mcp_server"]
}
}
}fray detect https://example.com
fray test https://example.com -c xss --max 10
fray payloads4,025+ total payloads across 40+ categories:
- A01: Broken Access Control (150+)
- A02: Cryptographic Failures (50+)
- A03: Injection (500+ - XSS, SQLi, XXE, SSTI, Command Injection)
- A04: Insecure Design (80+)
- A05: Security Misconfiguration (100+)
- A06: Vulnerable Components (450+ - WordPress CVEs)
- A07: Authentication Failures (200+)
- A08: Software/Data Integrity (70+)
- A09: Logging/Monitoring (30+)
- A10: SSRF (60+)
- M1-M10: Complete mobile security coverage (Android & iOS)
- LLM01: Prompt Injection (100+)
- LLM02-LLM10: AI/ML security testing
- API1-API10: Complete API security coverage (REST, GraphQL, SOAP)
- REST API auth bypass & user enumeration (150+)
- File upload bypass & web shell detection (200+)
- XML-RPC amplification & brute force (100+)
- XSS, SQLi, SSRF, Path Traversal, LDAP, XPath, CRLF, and more
See docs/owasp-complete-coverage.md for detailed breakdown.
IMPORTANT: Only test systems you own or have explicit permission to test. See LICENSE for full legal disclaimer.
Contributions welcome! See CONTRIBUTING.md
MIT License - See LICENSE
⭐ Star this repo if you find it useful!