fix: restrict entitlements used for helper.app#312734
Conversation
There was a problem hiding this comment.
Pull request overview
Restricts the entitlements applied during macOS codesigning for the Electron Helper.app bundle, aiming to avoid the macOS 26 Tahoe network-process crash loop reported in #312720.
Changes:
- Route
* Helper.appsigning to a dedicated entitlements plist instead of falling back to the main app entitlements. - Add
build/azure-pipelines/darwin/helper-entitlements.plistwith a minimal entitlement set (com.apple.security.cs.allow-jit).
Reviewed changes
Copilot reviewed 2 out of 2 changed files in this pull request and generated no comments.
| File | Description |
|---|---|
| build/darwin/sign.ts | Adds a helper-app-specific entitlements selection branch for Helper.app paths. |
| build/azure-pipelines/darwin/helper-entitlements.plist | Introduces a minimal entitlements plist intended for the Helper.app bundle. |
|
Build to publish on failure for testing https://monacotools.visualstudio.com/Monaco/_build/results?buildId=434082&view=results |
|
Although the fix here is the correct path, I wanted to understand why we couldn't catch the crash during manual testing on our devices and only users started reporting after the release. As a first step I created a VM that was not corp managed and there the crash was reliable, this gives some definitive proof to MDM based management was relaxing checks on our corp devices Running https://gist.github.com/deepak1556/bbfcd0b5e56a05ff5a2afd9ea4285441 on both VM and corp machine yielded similar result, which means user space static validation matches so something at the kernel level was different for the runtime checks to fail. Next decided to check amfi related settings and the only one that stood out was sysctl security.mac.amfi | sort
The AMFI kernel extension is closed source however we can run DTrace on certain probes to see how the code signature path works between these devices, the probes I setup were This resulted in the following paths when launching a fresh instance of the app whose CDHash was not cached in the Tickets database. VM: Corp machine: After CoreTrust fails, corp machine finds the CDHash in a loadable trust cache and proceeds. VM has no trust cache entry ends up in immediate failure. Now we are getting close, sudo log show --last boot --predicate 'composedMessage CONTAINS[cd] "trust cache" OR composedMessage CONTAINS[cd] "trustcache" OR composedMessage CONTAINS[cd] "loadTrustCache"' --info --debug | head -30Corp machine loads trust caches at boot: MDM enrollment (Intune in our case) causes |
51eeba3 to
7c7f487
Compare
blocks-ci screenshots changedReplace the contents of Updated blocks-ci-screenshots.md<!-- auto-generated by CI — do not edit manually -->
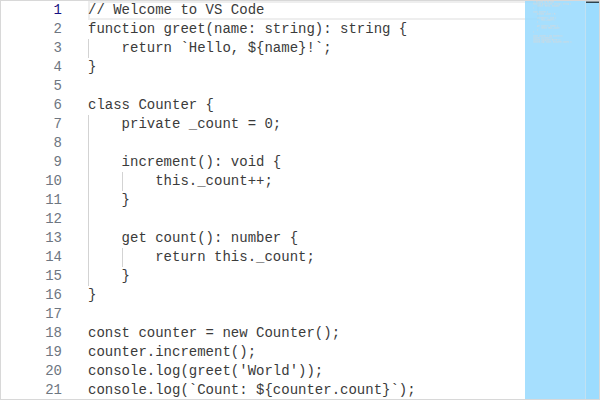
#### editor/codeEditor/CodeEditor/Dark
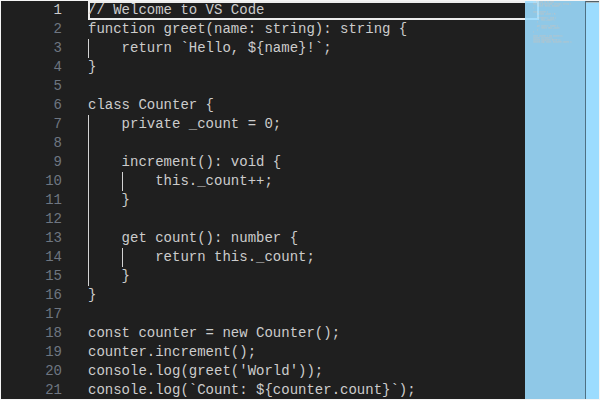
#### editor/codeEditor/CodeEditor/Light
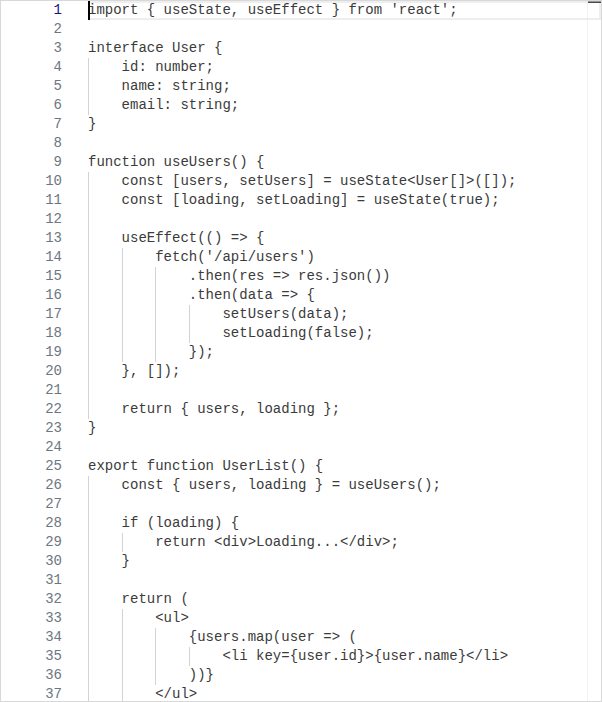
#### editor/inlineChatZoneWidget/InlineChatZoneWidget/Dark
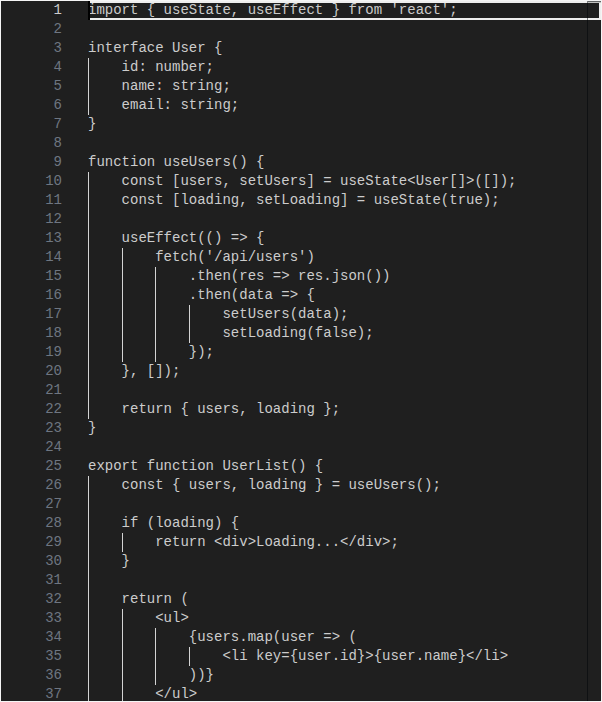
#### editor/inlineChatZoneWidget/InlineChatZoneWidget/Light
#### editor/inlineChatZoneWidget/InlineChatZoneWidgetTerminated/Dark
#### editor/inlineChatZoneWidget/InlineChatZoneWidgetTerminated/Light
 |
📬 CODENOTIFYThe following users are being notified based on files changed in this PR: @lszomoruMatched files:
|
For #312720